What is VirTool:JS/Obfuscator.HO?
VirTool:JS/Obfuscator.HO is regarded as a high-risk Trojan horse. It has been used by cyber criminals to steal computer users’ personal information or important data. Usually, it cannot propagate through system via replicating by itself and infecting other files. However, it can easily invade into your system when you get in touch with spam emails, freeware, online games, unreliable sites, or strange links, etc.
Just like TrojanSpy:Win32/Nivdort.DJ, it is capable of creating vicious files, modifying or deleting files on your computer, downloading unwanted programs to consume your system CPU, indirectly drop down system performance, or even causing blue screen and system halted. What’s worse, it is in a position to help hackers to access and control your system via opening a backdoor which is also used by other cyber criminals to spread adware, virus, malware, ransowmare, or worms, etc.
How to Guard against VirTool:JS/Obfuscator.HO?
VirTool:JS/Obfuscator.HO can hides itself within seemingly harmless contents. Once installed clicked, or visited, it will straight to lands on your computer. As a result, you should be very cautious about your every action online. Certainly, the better ways is to stay away from the suspicious contents mentioned above. In addition, you also should install a powerful anti-malware or anti-virus programs to protect your computer and remember to fix all system security holes or vulnerabilities in time.
Methods to Remove VirTool:JS/Obfuscator.HO from Your Computer
VirTool:JS/Obfuscator.HO is so risky that you had better to get rid of it with safe and practical methods. In the next part, you can see two removal guides. One is manual guide; the other is automatic guide (SpyHunter). You can choice one according to your situation.
Mehod 1: Similar Video to Remove VirTool:JS/Obfuscator.HO
Method 2: Manual Removal Guide for VirTool:JS/Obfuscator.HO
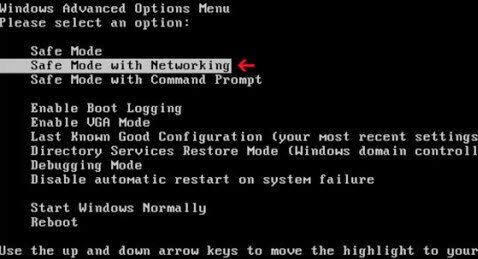
Step 1: Close all the running process on your computer and backup your important data and registry before manually removing this threat.
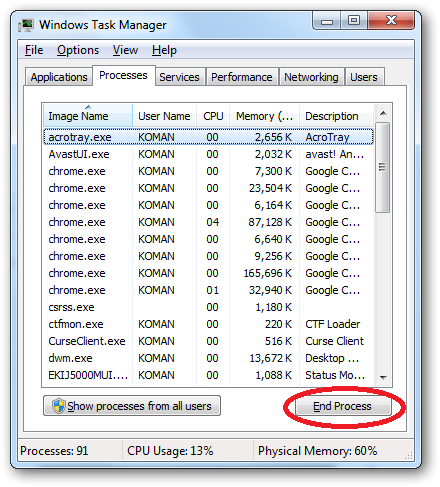
Step3. Close all the processes of VirTool:JS/Obfuscator.HO in Windows Task Manager
1. Press Ctrl+sShift+Esc or Ctrl+Alt+Delete to open Windows Task Manager,
2. Look for malicious processes relevant to VirTool:JS/Obfuscator.HO,
3. Click End process.
Step 4: Navigate to the local disk C, find out and delete all malicious files created by VirTool:JS/Obfuscator.HO.
%Temp%\random.exe
%Program Files%\random.exe
%UserProfile%\Desktop\.lnk
%UserProfile%\Start Menu\.lnk
%UserProfile%\ApplicationData\Microsoft\InternetExplorer\QuickLaunch\random.exe
Step5. Switch to Registry Editor and delete all the files relevant to VirTool:JS/Obfuscator.HO.
1. Click on Win+ R key at the same time to open Run Commend Box. Open Registry Editor by typing “regedit” in Runbox and clicking OK.
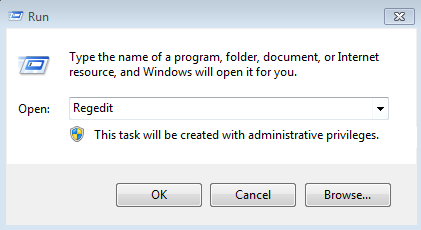
2. Glance through registry entries and find out all listed hazardous items. Right click on them and click Delete to remove.
Attention: If you are not confident to take the manual guide, you can take consideration to remove VirTool:JS/Obfuscator.HO automatically with SpyHunter.
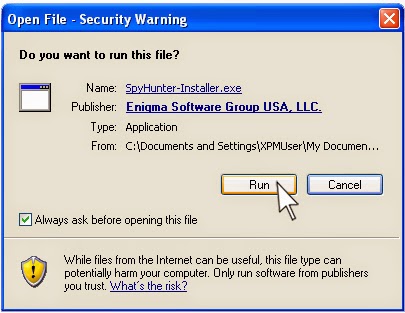
Method 3: Automatic Removal Guide for VirTool:JS/Obfuscator.HO
SpyHunter is a real-time anti-malware program and automatic removal tool, which is able to protect your computer from malware, spyware, worms, etc.
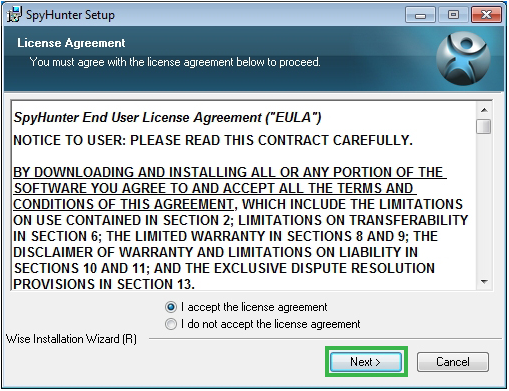
Step 2. Click Run to install the files related to SpyHunter step by step.
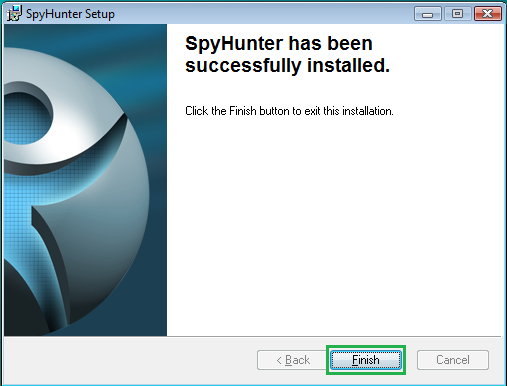
Step 3. Scan and detect your PC system automatically with SpyHunter when finishing the installation.


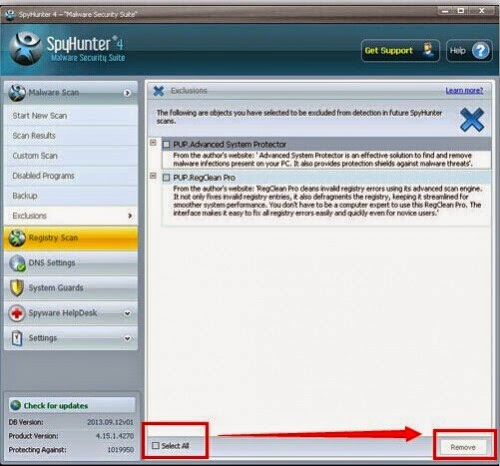
Step 4. Check Select All, and then click Remove button to remove all threats in your PC.
Recommendation:
It is not enough to only remove VirTool:JS/Obfuscator.HO because there are many falsified system configuration in computer due to this infection. As a result, it is necessary for you to clear up and optimize your system after removing it.
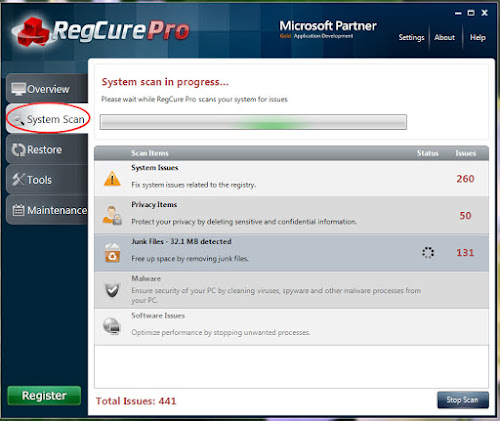
(>>>RegCure Pro is a perfect program to help you clear up all unwanted files or configurations as well as optimize your system)
Step1. Download RegCure Pro via hitting teh icon below.
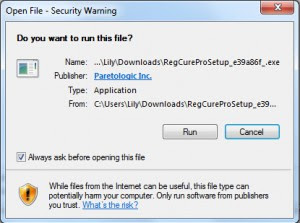
Step2. Hit Run to install the relevant grogram step by step.
Step3. Scan computer system to find out suspicious files by going on Overview.

Note: If you are a novice in PC operation and have no confidence to remove this Trojan horse with manual process, you can install SpyHunter to help you dealt with it as well as protect your PC from it and similar threats. Moreover, you can opertimize your system and restore files with RegCure Pro after getting rid of all threats.




